Security Starts with Every Patch
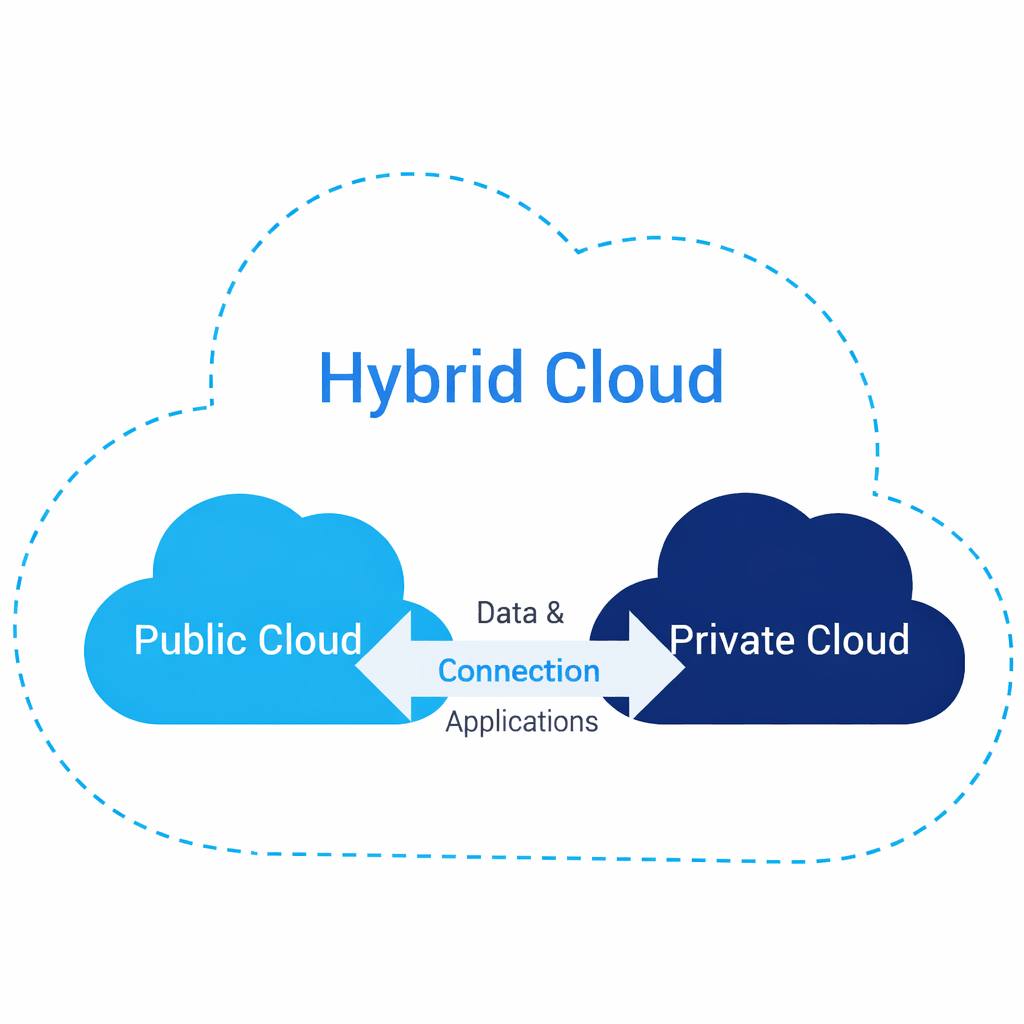
Cloud security and migration enable organizations to move applications and data to the cloud safely, reliably, and with minimal business disruption. A successful program starts with clear goals—cost, agility, resilience, compliance—and builds a security foundation that applies consistently across on-prem and cloud environments.
Key elements include zero-trust access (strong identity, least privilege, MFA), network segmentation and secure connectivity, encryption and key management, continuous monitoring/logging, and standardized guardrails using policy-as-code. Migration is executed in controlled phases—assessment, wave planning, pilot, and scale—using the right approach per application (rehost, replatform, refactor) while validating performance, recovery, and compliance.
Why you Should Choose Our Services
We deliver proactive, reliable, and secure IT solutions tailored to your business needs. Our experts monitor, manage, and optimize your infrastructure around the clock.
- Take a professional approach
- Provide unhindered support 24/7
- Offer full-cycle IT services
- We take our job seriously
- Our team is qualified

Services
© All Copyright 2024 by Ovatheme.com